Fake iCloud Storage Alerts Surge as Phishing Campaign Targets Apple Users
- 4 hours ago
- 3 min read
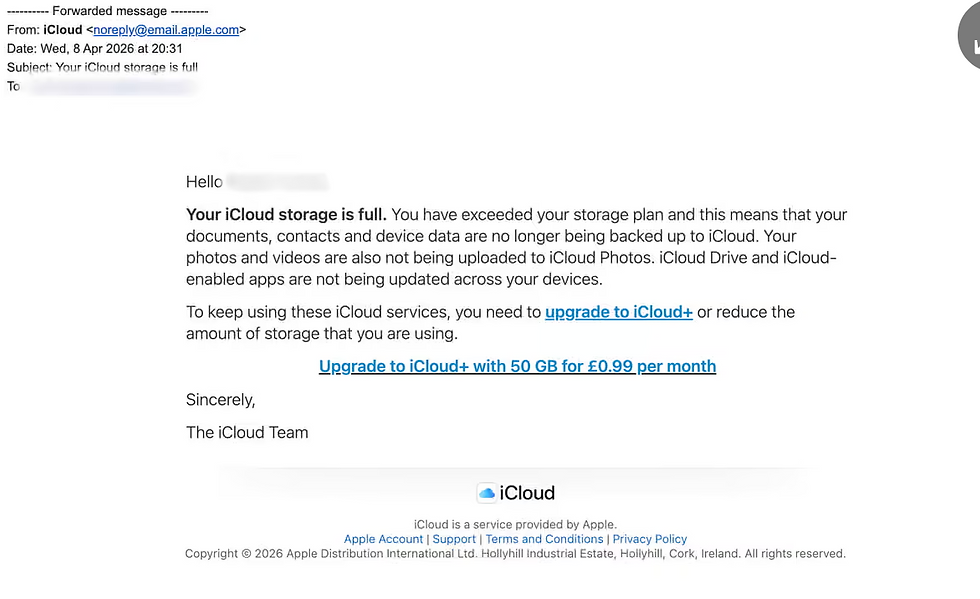
A new wave of phishing attacks is exploiting one of the most familiar digital annoyances: iCloud storage warnings. Security researchers say attackers are impersonating Apple billing alerts to trick users into handing over credentials, payment details, and ultimately control of their Apple IDs.
The campaign hinges on a simple but effective tactic. Users receive emails claiming their iCloud storage is full, followed by escalating warnings that their accounts have been blocked or that photos and videos will soon be deleted. The messages push urgency, directing recipients to click a button to “upgrade” storage or update payment information.
In reality, the links lead to phishing pages designed to closely mimic Apple’s login and billing interfaces.

Why This Phishing Scam Works So Well
Unlike generic phishing attempts, this campaign aligns with real user behavior. Apple frequently sends legitimate storage notifications, which lowers suspicion when fraudulent versions arrive.
According to Chance Caldwell, Senior Director of the Phishing Defense Center at Cofense, attackers are deliberately exploiting that familiarity.
"Subscription based services have become prime phishing targets because users are conditioned to resolve billing issues immediately, which creates ideal conditions for threat actors to feign urgency. The ultimate goal is often not the initial payment, but to gain full Apple ID compromise, allowing attackers to pivot into broader identity theft and cross-platform account takeovers. Campaigns such as this one succeed because they mirror real user experiences that will catch people with their guard down unless they have the knowledge needed to verify such requests."
That alignment between real notifications and fake ones is what makes this campaign particularly dangerous for both consumers and enterprise users managing Apple devices.
Inside the Attack Chain
Once a victim clicks the link, the attack unfolds in stages:
Credential Harvesting: Fake login pages capture Apple ID usernames and passwords
Financial Data Theft: Victims may be prompted to enter payment details under the guise of a storage upgrade
Account Takeover: Attackers gain access to iCloud data including photos, files, and backups
Secondary Exploitation: Stolen credentials can be reused across other services or sold on criminal marketplaces
Security analysts note that the initial payment request is often a distraction. The real prize is persistent access to identity-linked accounts.
Red Flags in Fake iCloud Emails
While the phishing emails are increasingly polished, several indicators still stand out:
Suspicious sender domains that do not match Apple infrastructure
Poor grammar or inconsistent wording
Threat-heavy language pushing immediate action
Links that redirect to non-Apple domains
Claims of account deletion within unrealistic timeframes
Some campaigns also send follow-up emails labeled as “final warnings” to increase pressure.
Enterprise Risk Beyond Consumers
While this campaign primarily targets individuals, the implications extend into enterprise environments. Employees using Apple devices for work may inadvertently expose corporate data if their Apple IDs are compromised.
This is especially relevant as organizations continue adopting BYOD policies and cloud-synced workflows tied to personal accounts.
How to Protect Against iCloud Phishing Attacks
Security teams recommend a straightforward but critical set of defenses:
Never click links in unsolicited billing or storage emails
Verify storage status directly through device settings
Access Apple services only through official apps or trusted URLs
Enable multi-factor authentication on Apple IDs
Report suspicious emails to Apple and internal security teams
If credentials or payment details are submitted, immediate action is required. Users should reset passwords, enable additional security controls, and contact financial institutions to prevent fraud.
The Bigger Trend: Identity as the Attack Surface
This campaign reflects a broader shift in cybercrime. Attackers are moving away from malware-heavy tactics and focusing on identity compromise as the fastest path to valuable data.
Cloud accounts, subscription services, and digital identities are now prime entry points. The iCloud phishing surge is just one example of how attackers are blending social engineering with platform familiarity to scale attacks.
For security leaders, the takeaway is clear. Technical controls alone are not enough. User awareness, identity protection, and verification workflows are now central to defending modern environments.


